What is the difference between dirty pipe and dirty cow
Dirty Pipe and Dirty COW, the differences
What makes this vulnerability even more risky is the ease with which it can be exploited. In fact, Max Kellermann compared the Dirty Pipe vulnerability to CVE-2016-5195, better known as Dirty COW, specifying that Dirty Pipe is easier to exploit.
What is a dirty pipe
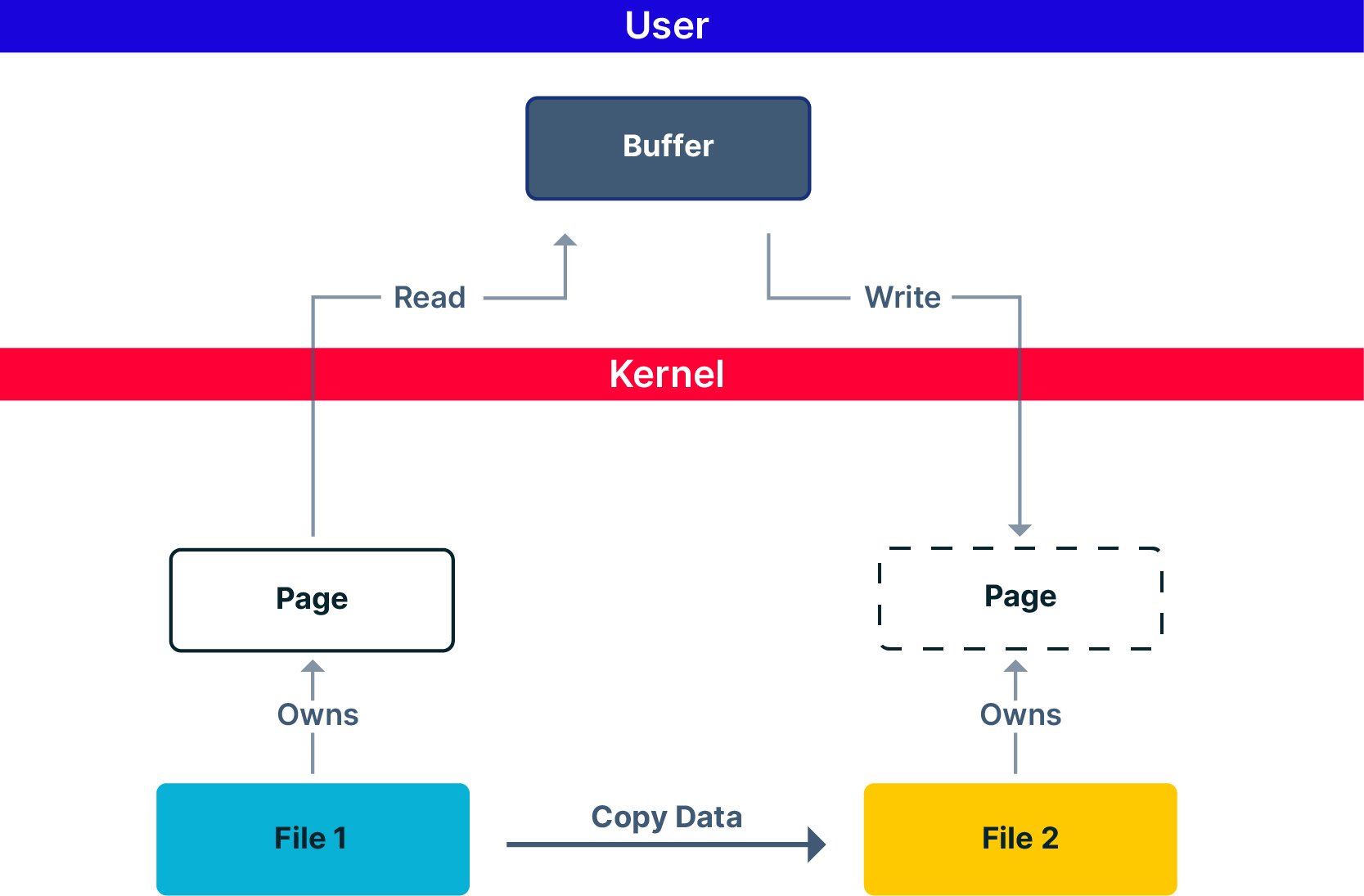
The Dirty Pipe exploit allows apps to manipulate Linux pipes so that the application can insert its data into a page of memory. This makes it easy for the attacker to either replace the contents of a file that the user is trying to access or even get full control of the user's system.
What is the dirty cow vulnerability
Dirty COW was a vulnerability in the Linux kernel. It allowed processes to write to read-only files. This exploit made use of a race condition that lived inside the kernel functions which handle the copy-on-write (COW) feature of memory mappings.
Am I vulnerable to dirty pipe
The easiest way to check whether your system is vulnerable is to see which version of the Linux kernel it uses by running the command uname -r . A system is likely to be vulnerable if it has a kernel version higher than 5.8, but lower than 5.16.
What is the impact of dirty pipe
Dirty Pipe danger to containers
According to McCune, the Dirty Pipe exploit allows attackers to violate that security guarantee because they can make changes to the base image from inside a container. This will impact all other containers that are started from the same image.
Why is it called Dirty COW
Untrusted users can exploit it to gain highly privileged write-access rights to memory mappings that would normally be read-only. More technical details about the vulnerability and exploit are available below. Using the acronym derived from 'copy-onwrite', some researchers have dubbed the vulnerability 'Dirty COW'.
What does Dirty COW mean
Dirty COW is a computer security vulnerability that affects all Linux-based systems, including Android. Here's how you can protect yourself from it.
What is a dirty Pipe
The Dirty Pipe exploit allows apps to manipulate Linux pipes so that the application can insert its data into a page of memory. This makes it easy for the attacker to either replace the contents of a file that the user is trying to access or even get full control of the user's system.
What is the CVE score for dirty Pipe
7.8
This vulnerability allows attackers to overwrite read-only or immutable files and escalate their privileges in the victim's system. CVE-2022-0847 vulnerability is named Dirty Pipe and has a CVSS score of 7.8 (high) [2].
What is the Dirty COW vulnerability
Dirty COW was a vulnerability in the Linux kernel. It allowed processes to write to read-only files. This exploit made use of a race condition that lived inside the kernel functions which handle the copy-on-write (COW) feature of memory mappings.
What is the cause of Dirty COW vulnerability
The Dirty COW vulnerability is a privilege escalation vulnerability, and it is caused by a race condition found in the way the Linux kernel's memory subsystem handles the copy-on-write breakage of private, read-only memory mappings.
What is Dirty COW in cyber security
Dirty COW, officially known as "CVE-2016-5195", is a privilege escalation vulnerability found in the Linux Kernel. It is defined as "a race condition that was found in the Linux kernel's memory subsystem handled the copy-on-write (COW) breakage of private read-only memory mappings"
What does a CVE score of 10 mean
CVSS attempts to assign severity scores to vulnerabilities, allowing responders to prioritize responses and resources according to threat. Scores are calculated based on a formula that depends on several metrics that approximate ease and impact of an exploit. Scores range from 0 to 10, with 10 being the most severe.
What is the CVE for Dirty COW
Dirty COW (CVE-2016-5195)
How is CVE score calculated
CVSS scores are calculated using a formula consisting of vulnerability-based metrics. A CVSS score is derived from scores in these three groups: Base, Temporal and Environmental. Scores range from zero to 10, with zero representing the least severe and 10 representing the most severe.
What is the highest CVE score
Scores range from 0 to 10, with 10 being the most severe. While many utilize only the CVSS Base score for determining severity, temporal and environmental scores also exist, to factor in availability of mitigations and how widespread vulnerable systems are within an organization, respectively.
What is Dirty COW exploit CVE-2016-5195
CVE-2016-5195 Detail
c in the Linux kernel 2. x through 4. x before 4.8. 3 allows local users to gain privileges by leveraging incorrect handling of a copy-on-write (COW) feature to write to a read-only memory mapping, as exploited in the wild in October 2016, aka "Dirty COW."
What is CVE vs CVSS score
The CVE represents a summarized vulnerability, while the Common Vulnerability Scoring System (CVSS) assesses the vulnerability in detail and scores it, based on several factors.
What is the difference between CVE and vulnerability
CVE stands for Common Vulnerabilities and Exposures. CVE is a glossary that classifies vulnerabilities. The glossary analyzes vulnerabilities and then uses the Common Vulnerability Scoring System (CVSS) to evaluate the threat level of a vulnerability.
Do all vulnerabilities have a CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
What is CCE vs CVE
CVE provides this capability for information security vulnerabilities, CCE assigns a unique, common identifier to a particular security-related configuration issue. The name of the imported file. The type of the list, that is, if it is a CVE or CCE list.
What is CWE vs CVE
Whereas the CVE logs real-world instances of vulnerabilities and exposures in specific products, the CWE lists and defines weaknesses commonly seen in digital products. The CWE does not refer to one particular example but provides definitions for widely seen defects.
What is CVE vs CWE example
CVE stands for Common Vulnerabilities and Exposures. When you see CVE, it refers to a specific instance of a vulnerability within a product or system. For example, Microsoft Outlook Elevation of Privilege Vulnerability is CVE-2023-23397. CWE stands for Common Weakness Enumeration.
What is the difference between CVS and CVE
Differences between CVSS and CVE
CVSS is the overall score assigned to a vulnerability. CVE is simply a list of all publicly disclosed vulnerabilities that includes the CVE ID, a description, dates, and comments. The CVSS score is not reported in the CVE listing – you must use the NVD to find assigned CVSS scores.
What is CVE and CWE in cyber security
In other words, CVE is a list of known instances of vulnerability for specific products or systems, while CWE acts as a dictionary (so to speak) of software vulnerability types. The National Vulnerability Database (NVD) actually uses CWEs to score CVEs.