What is an example of a CVE vulnerability
One example would be a loosely secured cloud storage system that allows attackers to access sensitive data. Another example would be an open network port on a server which is further exploited through the installation of command and control malware.
What is a CVE in cybersecurity
Common Vulnerabilities and Exposures (CVE) is a catalog of known security threats. The catalog is sponsored by the United States Department of Homeland Security (DHS), and threats are divided into two categories: vulnerabilities and exposures.
How does CVE work
CVE does this by creating a standardized identifier for a given vulnerability or exposure. CVE identifiers (also called CVE names or CVE numbers) allow security professionals to access information about specific cyber threats across multiple information sources using the same common name.
What are CVE identifiers
CVE Identifier (CVE ID) A unique, alphanumeric identifier assigned by the CVE Program. Each identifier references a specific vulnerability. A CVE ID enables automation and multiple parties to discuss, share, and correlate information about a specific vulnerability, knowing they are referring to the same thing.
What are 3 examples of vulnerability
11 examples of vulnerabilityTelling someone when they've upset you, respectfully but honestly.Sharing something personal about yourself that you normally wouldn't.Admitting to mistakes you have made in the past.Being willing to feel difficult emotions like shame, grief, or fear.
What are 3 example of vulnerabilities
Vulnerability Examples
Any susceptibility to humidity, dust, soiling, natural disaster, poor encryption, or firmware vulnerability.
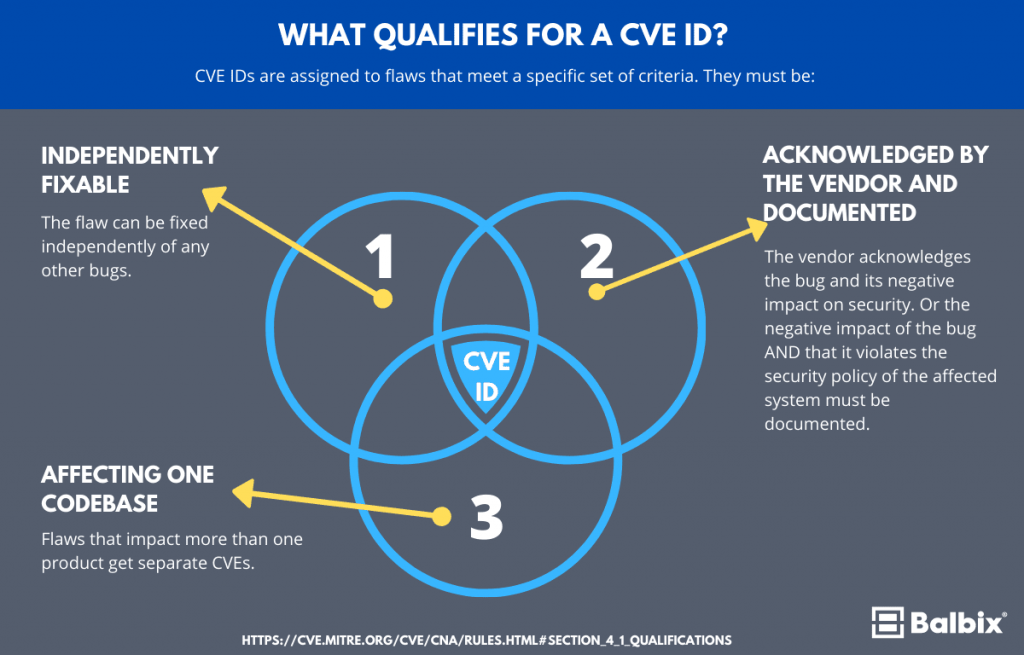
Do all vulnerabilities have a CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
How does a vulnerability become a CVE
The reporter requests a CVE ID, which is then reserved for the reported vulnerability. Once the reported vulnerability is confirmed by the identification of the minimum required data elements for a CVE Record, the record is published to the CVE List.
Who creates a CVE for vulnerability
The Mitre Corporation
CVEs are assigned by a CVE Numbering Authority (CNA). While some vendors acted as a CNA before, the name and designation was not created until February 1, 2005. there are three primary types of CVE number assignments: The Mitre Corporation functions as Editor and Primary CNA.
What are elements of a CVE
The CVE element contains the CVE ID of the entry. The References element contains CVE's cross-references. There can be one or more Reference elements. Within a Reference element, the Description is used for the reference name (CVE-style "SOURCE:name"), and the URL element is used for the URL.
What are 5 example of vulnerability
To illustrate the principles above, here are 11 specific examples of vulnerability: Telling someone when they've upset you, respectfully but honestly. Sharing something personal about yourself that you normally wouldn't. Admitting to mistakes you have made in the past.
What are the 4 main types of vulnerability examples
The different types of vulnerability
According to the different types of losses, the vulnerability can be defined as physical vulnerability, economic vulnerability, social vulnerability and environmental vulnerability.
What is the most common CVE
CVE-2022-22965: The most popular CVE reported in 2022 (also known as Spring4Shell) is an extremely high-impact Injection vulnerability in Spring Framework that allows attackers to make changes remotely to a target system.
Does CVE mean vulnerability
Common Vulnerabilities and Exposures
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.
What is CVE format
A CVE ID is a unique, alphanumeric identifier assigned by the CVE Program. Each identifier references a specific vulnerability. CVE IDs have the following format: CVE prefix + Year + Arbitrary Digits. The “Year” portion is the year that the CVE ID was reserved or the year the vulnerability was made public.
How many CVE vulnerabilities are there
NVD Contains
| CVE Vulnerabilities | 220836 |
|---|---|
| Checklists | 617 |
| US-CERT Alerts | 249 |
| US-CERT Vuln Notes | 4486 |
| OVAL Queries | 10286 |