What is base score in vulnerability
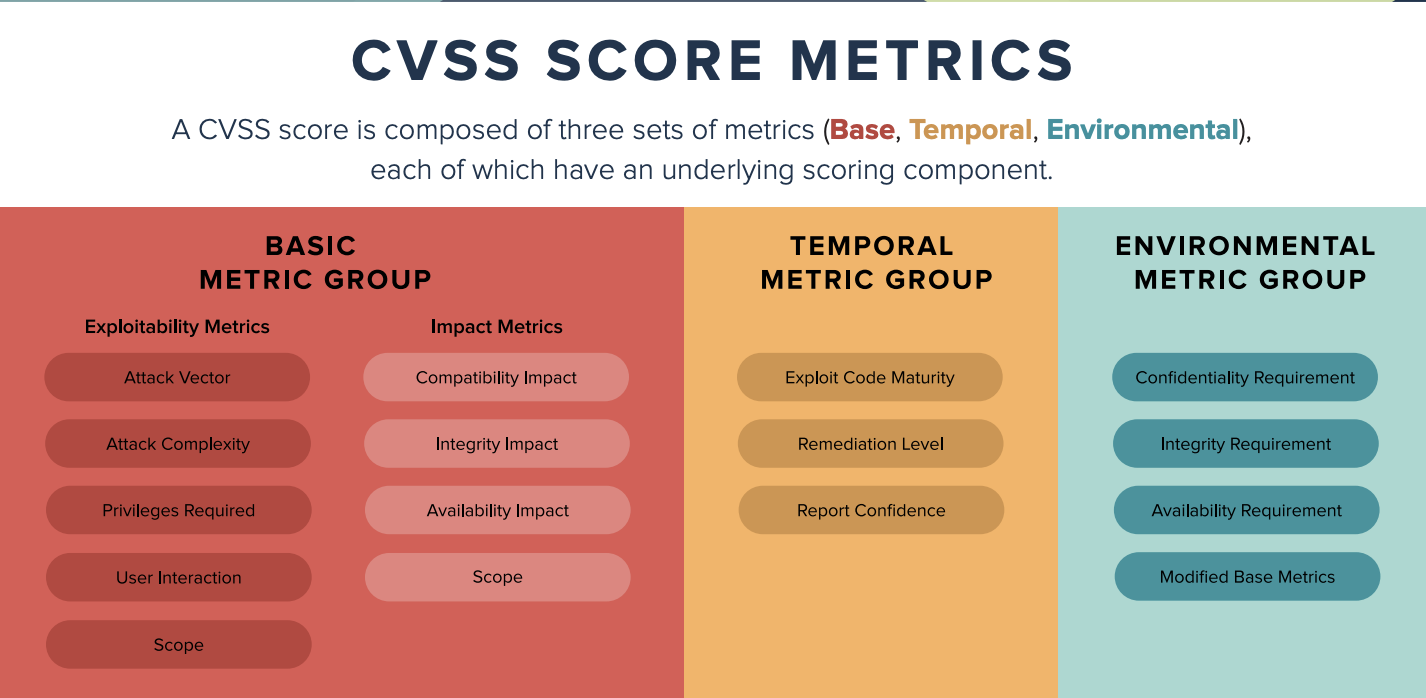
CVSS is composed of three metric groups: Base, Temporal, and Environmental. The Base Score reflects the severity of a vulnerability according to its intrinsic characteristics which are constant over time and assumes the reasonable worst case impact across different deployed environments.
What does a CVE score of 10 mean
CVSS attempts to assign severity scores to vulnerabilities, allowing responders to prioritize responses and resources according to threat. Scores are calculated based on a formula that depends on several metrics that approximate ease and impact of an exploit. Scores range from 0 to 10, with 10 being the most severe.
What is cvssv3 base score
NVD Vulnerability Severity Ratings
| CVSS v2.0 Ratings | CVSS v3.0 Ratings | |
|---|---|---|
| Severity | Base Score Range | Base Score Range |
| Low | 0.0-3.9 | 0.1-3.9 |
| Medium | 4.0-6.9 | 4.0-6.9 |
| High | 7.0-10.0 | 7.0-8.9 |
What is the difference between CVE base score and temporal score
Base Metrics do not change over time – they remain the same throughout the lifetime of a vulnerability. Temporal Metrics, on the other hand, change over time as a result of activities conducted by both software vendors and hackers. Temporal metrics are sometimes, but not always, reported in the NVD.
What is a base score
The base score operates using a 0 to 10 scale attributed to inherent vulnerabilities of software unaffected by time or environmental factors.
How is CVE score calculated
CVSS scores are calculated using a formula consisting of vulnerability-based metrics. A CVSS score is derived from scores in these three groups: Base, Temporal and Environmental. Scores range from zero to 10, with zero representing the least severe and 10 representing the most severe.
What is the score of CVE 2007 4559
CVE-2007-4559 allows for the execution of arbitrary code. Although CVE-2007-4559's CVSS score of 5.1 indicates that it is a medium severity vulnerability, Trellix claims that its attack is quite simple and may be exploited with as few as six lines of code.
What is a CVSS base score of 10
CVSS Qualitative Ratings
| CVSS Score | Qualitative Rating |
|---|---|
| 0.1 – 3.9 | Low |
| 4.0 – 6.9 | Medium |
| 7.0 – 8.9 | High |
| 9.0 – 10.0 | Critical |
How is CVSS base score calculated
The only requirement for categorizing a vulnerability with a CVSS score is the completion of the Base score components: the Exploitability subscore, the Impact subscore and the Scope subscore. These scores are used to calculate the overall Base score using a formula that weights each subscore.
What is the difference between base and temporal
Base Metrics contain qualities that are intrinsic to any given vulnerability that do not change over time or in different environments. Temporal Metrics contain characteristics of a vulnerability which evolve over the lifetime of vulnerability.
How is a CVSS base score calculated
The only requirement for categorizing a vulnerability with a CVSS score is the completion of the Base score components: the Exploitability subscore, the Impact subscore and the Scope subscore. These scores are used to calculate the overall Base score using a formula that weights each subscore.
What is CWE or CVE score
While both standards play a critical role in secure software development, they have different purposes. In summary, CVE is a standard for identifying and naming specific vulnerabilities, while CWE is a standard for classifying and describing the types of weaknesses that can lead to vulnerabilities.
What is CVE ID and CVSS score
CVSS is the overall score assigned to a vulnerability. CVE is simply a list of all publicly disclosed vulnerabilities that includes the CVE ID, a description, dates, and comments. The CVSS score is not reported in the CVE listing – you must use the NVD to find assigned CVSS scores.
What is the CVE score of log4j vulnerability
a 10 out of 10
It's described as a zero-day (0 day) vulnerability and rated the highest severity under the Common Vulnerability Scoring System (CVSS; CVE-2021-44228). It was rated a 10 out of 10 on the CVSS, due to the potential impact that it can have if leveraged by attackers.
Is CVSS the same as CVE
Differences between CVSS and CVE
CVSS is the overall score assigned to a vulnerability. CVE is simply a list of all publicly disclosed vulnerabilities that includes the CVE ID, a description, dates, and comments. The CVSS score is not reported in the CVE listing – you must use the NVD to find assigned CVSS scores.
Does log4j 1.2 17 have vulnerability
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Does CVE mean vulnerability
Common Vulnerabilities and Exposures
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.
Is Log4j 2.17 0 vulnerable
3 or 2.17. 0: from these versions onwards, only the JAVA protocol is supported in JNDI connections. Note that only the log4j-core JAR file is impacted by this vulnerability. Applications using only the log4j-api JAR file without the log4j-core JAR file are not impacted by this vulnerability.
Does Log4j 1.2 14 have vulnerability
Affected versions of this package are vulnerable to Deserialization of Untrusted Data. JMSSink in all versions of Log4j 1. x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to.
Is Log4j 2.17 1 safe
1 can probably wait. A number of security professionals say that the latest vulnerability in Apache Log4j, disclosed on Tuesday, does not pose an increased security risk for the majority of organizations. As a result, for many organizations that have already patched to version 2.17.
Is Log4j 2.12 4 vulnerable
2 and 2.12. 4) are vulnerable to a remote code execution (RCE) attack where an attacker with permission to modify the logging configuration file can construct a malicious configuration using a JDBC Appender with a data source referencing a JNDI URI which can execute remote code.
Is Log4j 1.2 17 vulnerable or not
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Is Log4j 1.2 7 vulnerable
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
Is Log4j 2.16 still vulnerable
December 20, 2021
Log4j 2.17 has been released to address a Denial of Service (DoS) vulnerability found in v2. 16 and earlier. Log4j 2.16 and earlier does not always protect from infinite recursion in lookup evaluation, which can lead to DoS attacks. This is considered a High (7.5) vulnerability on the CVSS scale.
Is Log4j 1.2 17 Safe
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.