What does CVE mean in cyber security
Common Vulnerabilities and Exposures
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.
What is a CVE and how is it used
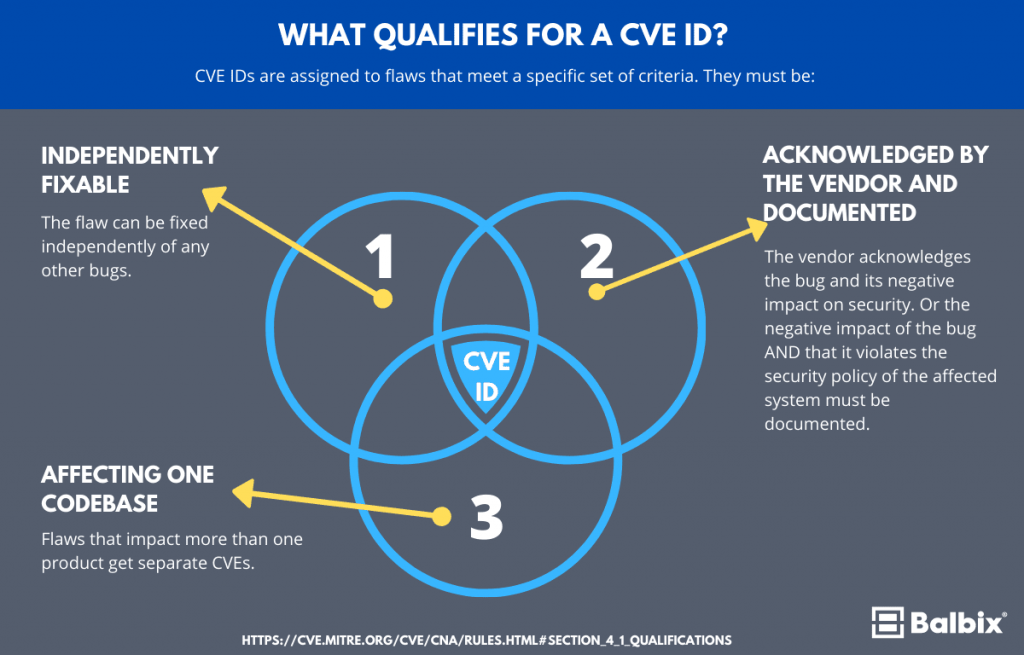
Overview. CVE, short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws. When someone refers to a CVE, they mean a security flaw that's been assigned a CVE ID number. Security advisories issued by vendors and researchers almost always mention at least one CVE ID.
What is an example of a CVE vulnerability
One example would be a loosely secured cloud storage system that allows attackers to access sensitive data. Another example would be an open network port on a server which is further exploited through the installation of command and control malware.
What is CVE vulnerability scan
The Common Vulnerabilities and Exposures (CVE) system identifies all vulnerabilities and threats related to the security of information systems. To do this, a unique identifier is assigned to each vulnerability. Test for free the CVE Scanner Request a demo.
Why do we use CVE
It allows organizations to keep track of and prioritize vulnerabilities, compare their severity, and track their cybersecurity posture over time. The CVE has been operating since 1999 and is run by the MITRE Corporation. It is important for risk management, vulnerability identification, and cybersecurity strategy.
Who creates CVE
the MITRE corporation
Founded in 1999, the CVE program is maintained by the MITRE corporation and sponsored by the U.S. Department of Homeland Security (DHS) and the Cybersecurity and Infrastructure Security Agency (CISA).
Why is CVE is very important
It allows organizations to keep track of and prioritize vulnerabilities, compare their severity, and track their cybersecurity posture over time. The CVE has been operating since 1999 and is run by the MITRE Corporation. It is important for risk management, vulnerability identification, and cybersecurity strategy.
Who creates a CVE for vulnerability
The Mitre Corporation
CVEs are assigned by a CVE Numbering Authority (CNA). While some vendors acted as a CNA before, the name and designation was not created until February 1, 2005. there are three primary types of CVE number assignments: The Mitre Corporation functions as Editor and Primary CNA.
What is the difference between CVE and vulnerability
CVE stands for Common Vulnerabilities and Exposures. CVE is a glossary that classifies vulnerabilities. The glossary analyzes vulnerabilities and then uses the Common Vulnerability Scoring System (CVSS) to evaluate the threat level of a vulnerability.
Do hackers use CVE
Can Hackers Use CVE to Attack My Organization The short answer is yes but many cybersecurity professionals believe the benefits of CVE outweigh the risks: CVE is restricted to publicly known vulnerabilities and exposures.
Why is CVE important
It allows organizations to keep track of and prioritize vulnerabilities, compare their severity, and track their cybersecurity posture over time. The CVE has been operating since 1999 and is run by the MITRE Corporation. It is important for risk management, vulnerability identification, and cybersecurity strategy.
Does every vulnerability have a CVE
In simple terms, we can state that 'All CVEs are vulnerabilities, but not all vulnerabilities have CVEs.
Do all vulnerabilities have CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
Is CVE good or bad
CVE entries are not a good source to rank products by their "overall security". The main idea behind the CVE system is to create unique identifiers for software vulnerabilities. It's not designed to be a complete and verified database of all known vulnerabilities in any product.
Do all vulnerabilities have a CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
What is the difference between CVE and CVSS
CVSS is the overall score assigned to a vulnerability. CVE is simply a list of all publicly disclosed vulnerabilities that includes the CVE ID, a description, dates, and comments. The CVSS score is not reported in the CVE listing – you must use the NVD to find assigned CVSS scores.
What are the 4 main types of vulnerability
Types of vulnerability include social, cognitive, environmental, emotional or military. In relation to hazards and disasters, vulnerability is a concept that links the relationship that people have with their environment to social forces and institutions and the cultural values that sustain and contest them.
What are the 5 categories of vulnerability
One classification scheme for identifying vulnerability in subjects identifies five different types-cognitive or communicative, institutional or deferential, medical, economic, and social. Each of these types of vulnerability requires somewhat different protective measures.
What are 5 example of vulnerability
To illustrate the principles above, here are 11 specific examples of vulnerability: Telling someone when they've upset you, respectfully but honestly. Sharing something personal about yourself that you normally wouldn't. Admitting to mistakes you have made in the past.
What are the 4 main types of vulnerability in cyber security
The four main types of vulnerabilities in information security are network vulnerabilities, operating system vulnerabilities, process (or procedural) vulnerabilities, and human vulnerabilities.
What are the 3 types of vulnerability
According to the different types of losses, the vulnerability can be defined as physical vulnerability, economic vulnerability, social vulnerability and environmental vulnerability.
What are the four 4 main types of vulnerability
Students will consider four principal vulnerability factors, namely: physical; social; economic; and environmental.
What are the 13 strands of vulnerability
Dorset Police outline 13 strands of vulnerability which is recognised nationally as:adults at risk.child abuse and neglect.female genital mutilation.honour based abuse.child sexual exploitation.human trafficking and modern day slavery.managing offenders.prostitution.
What are the 3 points of vulnerability
Vulnerability is a weakness which allows an attacker to reduce a system's information assurance. Vulnerability is the intersection of three elements : a system susceptibility or defect, attacker access to the defect, and attacker capability to exploit the defect.
How many CVE vulnerabilities are there
NVD Contains
| CVE Vulnerabilities | 220836 |
|---|---|
| Checklists | 617 |
| US-CERT Alerts | 249 |
| US-CERT Vuln Notes | 4486 |
| OVAL Queries | 10286 |