What is the purpose of CVE details
The mission of the CVE ® Program is to identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. There is one CVE Record for each vulnerability in the catalog.
What are the benefits of CVE
CVE benefits
CVE can help organizations improve their security defenses and, by doing so, ultimately reduce risk. For example, CVE makes it much easier to share information about vulnerabilities across and between organizations.
Why is CVE important in business
The CVE provides descriptions, dates, and other information about vulnerabilities. Additionally, the CVE sometimes lists the fixes or solutions for a specific vulnerability. This valuable information allows an IT team to learn more about a vulnerability so that they can come up with a solution.
What is the CVE list and how can it benefit network security
CVE was established to help any organization with IT infrastructure remain up-to-date with security threats identified across the broader cybersecurity community. By collecting hundreds to thousands of threats from across the globe, the CVE functions as a centralized repository for vulnerability management.
What is CVE vulnerability description
CVE, short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws. When someone refers to a CVE, they mean a security flaw that's been assigned a CVE ID number. Security advisories issued by vendors and researchers almost always mention at least one CVE ID.
Why are CWE and CVE important
Whereas the CVE logs real-world instances of vulnerabilities and exposures in specific products, the CWE lists and defines weaknesses commonly seen in digital products. The CWE does not refer to one particular example but provides definitions for widely seen defects.
What is the importance of vulnerability index
Conducting a vulnerability assessment has numerous benefits, including: Identifying vulnerabilities before hackers find them. VA scans all the network components, verifying whether they have weaknesses that cybercriminals can use to attack the organization.
What is the importance of security vulnerability
Vulnerability management enhances the overall security posture of your organization by recognizing key assets and where to prioritize efforts in order to reduce risk. Working together with other security teams, it helps prevent access and data exploitation by threat actors.
Is CVE good or bad
CVE entries are not a good source to rank products by their "overall security". The main idea behind the CVE system is to create unique identifiers for software vulnerabilities. It's not designed to be a complete and verified database of all known vulnerabilities in any product.
What is CVE technology
Common Vulnerabilities and Exposures (CVE) is a catalog of known security threats. The catalog is sponsored by the United States Department of Homeland Security (DHS), and threats are divided into two categories: vulnerabilities and exposures.
What is the importance of vulnerability identification
Vulnerability assessments can identify vulnerabilities in applications, systems, and network devices that attackers could exploit to gain unauthorized access to sensitive data. Organizations can reduce the risk of data breaches by identifying these vulnerabilities and protecting sensitive information.
Why are CVSS and CVE important
CVE is a glossary that classifies vulnerabilities. The glossary analyzes vulnerabilities and then uses the Common Vulnerability Scoring System (CVSS) to evaluate the threat level of a vulnerability. A CVE score is often used for prioritizing the security of vulnerabilities.
What is the importance of vulnerability in cyber security
A vulnerability in security refers to a weakness or opportunity in an information system that cybercriminals can exploit and gain unauthorized access to a computer system. Vulnerabilities weaken systems and open the door to malicious attacks.
What are the 4 main types of security vulnerability
Security Vulnerability TypesNetwork Vulnerabilities. These are issues with a network's hardware or software that expose it to possible intrusion by an outside party.Operating System Vulnerabilities.Human Vulnerabilities.Process Vulnerabilities.
Do all vulnerabilities have a CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
How does a vulnerability become a CVE
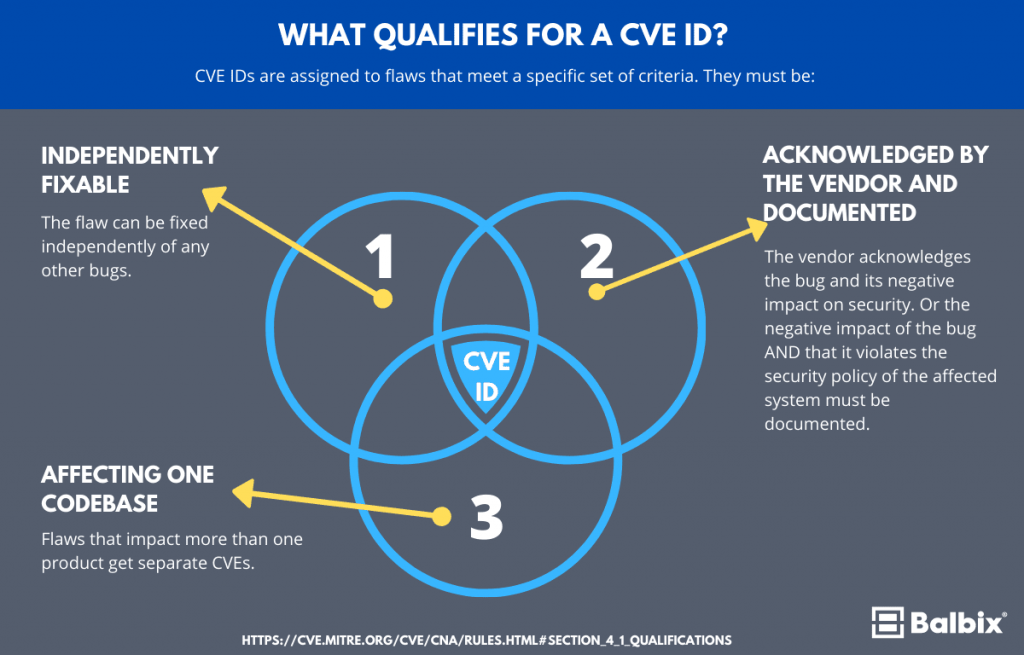
The reporter requests a CVE ID, which is then reserved for the reported vulnerability. Once the reported vulnerability is confirmed by the identification of the minimum required data elements for a CVE Record, the record is published to the CVE List.
What is CVE vulnerability scan
The Common Vulnerabilities and Exposures (CVE) system identifies all vulnerabilities and threats related to the security of information systems. To do this, a unique identifier is assigned to each vulnerability. Test for free the CVE Scanner Request a demo.
What is a CVE in cyber security
CVE, short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws. When someone refers to a CVE, they mean a security flaw that's been assigned a CVE ID number. Security advisories issued by vendors and researchers almost always mention at least one CVE ID.
Why is IT important to determine the vulnerability
Assessing the vulnerability of the built environment to hazards is extremely important in assessing potential consequences of an event and for mainstreaming disaster risk reduction into the local development planning process.
What is CVE in cyber security
CVE, short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws. When someone refers to a CVE, they mean a security flaw that's been assigned a CVE ID number. Security advisories issued by vendors and researchers almost always mention at least one CVE ID.
What is the 4 C’s in security
These four layers are Code security, Container security, Cluster security, and Cloud security. Let's take a deep dive into each of the C's to understand them better and also answer some of the most asked questions about the 4C's.
Does CVE mean vulnerability
Common Vulnerabilities and Exposures
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.
Who creates a CVE for vulnerability
The Mitre Corporation
CVEs are assigned by a CVE Numbering Authority (CNA). While some vendors acted as a CNA before, the name and designation was not created until February 1, 2005. there are three primary types of CVE number assignments: The Mitre Corporation functions as Editor and Primary CNA.
How does CVE scan work
Systems identify and highlight vulnerabilities, using data contained in the CVE database and other databases of known anomalies. Prioritization. Based on metrics programmed into the scanner, network devices use CVE data, threat intelligence and data science to assess issues and prioritize them for remediation.
Why is IT important to identify a vulnerable customer
For any organization, understanding and identifying vulnerable customers in a contact centre can be crucial for customer retention, preventing any risk of damage to these customers or the organization's own reputation.