What is meant by vulnerability detection
Vulnerability scanning is the process of identifying security weaknesses and flaws in systems and software running on them. This is an integral component of a vulnerability management program, which has one overarching goal – to protect the organization from breaches and the exposure of sensitive data.
What is vulnerable testing
Definition. A vulnerability assessment is the testing process used to identify and assign severity levels to as many security defects as possible in a given timeframe. This process may involve automated and manual techniques with varying degrees of rigor and an emphasis on comprehensive coverage.
What is web vulnerability detection
Description. Web Application Vulnerability Scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as Cross-site scripting, SQL Injection, Command Injection, Path Traversal and insecure server configuration.
Why is vulnerability detection important
Vulnerability scanning is important because of the many cybersecurity risks within a company. Vulnerabilities within a company's IT infrastructure can be breached by cybercriminals if those weaknesses go unnoticed. Despite the protective measures they have in place, enterprises experience data breaches.
What are the 4 main types of vulnerability in disaster
There are many aspects of vulnerability, arising from various physical, social, economic, and environmental factors.
What is vulnerability testing with example
It is one of the software testing techniques that is crucial for an application that demands high security and is more likely to attack or unauthorized access. For example, all POS applications, Banking applications, etc have high chances of malicious attacks as they deal with money.
What are the 4 main types of vulnerability
Types of vulnerability include social, cognitive, environmental, emotional or military. In relation to hazards and disasters, vulnerability is a concept that links the relationship that people have with their environment to social forces and institutions and the cultural values that sustain and contest them.
What are the 5 types of vulnerable
One classification scheme for identifying vulnerability in subjects identifies five different types-cognitive or communicative, institutional or deferential, medical, economic, and social. Each of these types of vulnerability requires somewhat different protective measures.
What can a vulnerability scanner detect
A vulnerability scanner enables organizations to monitor their networks, systems, and applications for security vulnerabilities. Most security teams utilize vulnerability scanners to bring to light security vulnerabilities in their computer systems, networks, applications and procedures.
What are the benefits of vulnerability testing
A vulnerability assessment can also help protect the integrity of assets in the event of any malicious code concealed in any of said assets. Vulnerability testing also helps reach and preserve compliance with any federal and international security regulations that may apply.
What are the 4 stages of identifying vulnerabilities
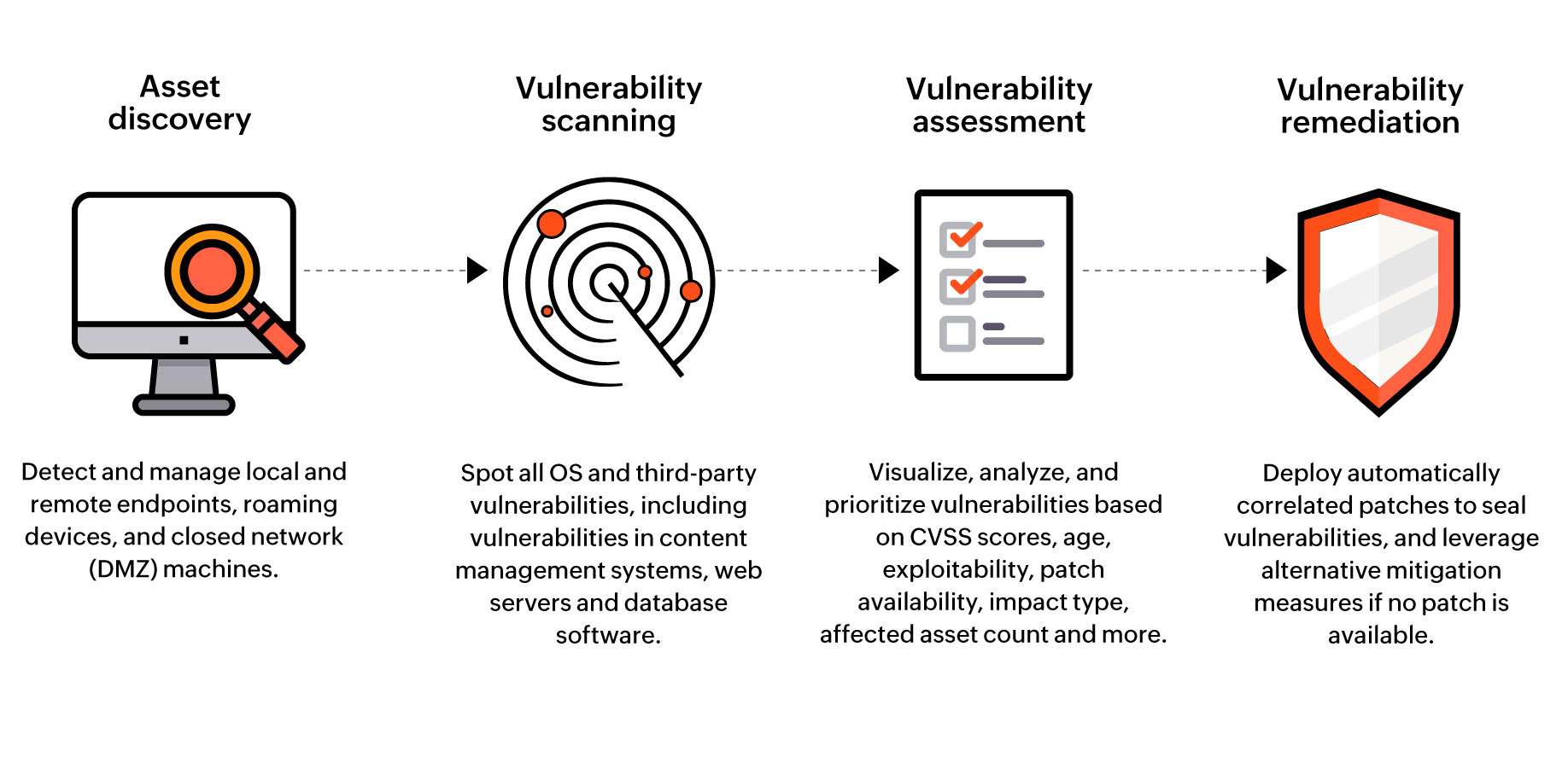
A 4-Step Vulnerability Management ProcessIdentification. A vulnerability management system continuously scans an environment against one or more databases of known vulnerabilities, with the objective of identifying vulnerable assets.Prioritization.Remediation.Verification and Reporting.
What are 3 examples of vulnerability
11 examples of vulnerabilityTelling someone when they've upset you, respectfully but honestly.Sharing something personal about yourself that you normally wouldn't.Admitting to mistakes you have made in the past.Being willing to feel difficult emotions like shame, grief, or fear.
What are the 4 main types of vulnerability examples
The different types of vulnerability
According to the different types of losses, the vulnerability can be defined as physical vulnerability, economic vulnerability, social vulnerability and environmental vulnerability.
What are the 5 categories of vulnerability
One classification scheme for identifying vulnerability in subjects identifies five different types-cognitive or communicative, institutional or deferential, medical, economic, and social. Each of these types of vulnerability requires somewhat different protective measures.
What are 5 example of vulnerability
To illustrate the principles above, here are 11 specific examples of vulnerability: Telling someone when they've upset you, respectfully but honestly. Sharing something personal about yourself that you normally wouldn't. Admitting to mistakes you have made in the past.
What are the 4 levels of vulnerability
The four continuous stages of identification, prioritization, remediation, and reporting are essential for an effective vulnerability management process. A vulnerability is a flaw or weakness in a system that, if exploited, would allow a user to gain unauthorized access to conduct an attack.
What is CVE scanning
The Common Vulnerabilities and Exposures (CVE) system identifies all vulnerabilities and threats related to the security of information systems. To do this, a unique identifier is assigned to each vulnerability. Test for free the CVE Scanner Request a demo.
How do hackers scan for vulnerabilities
Scanning can be considered a logical extension (and overlap) of active reconnaissance that helps attackers identify specific vulnerabilities. It's often that attackers use automated tools such as network scanners and war dialers to locate systems and attempt to discover vulnerabilities.
What is a goal of vulnerability testing
Vulnerability testing aims to discover security weaknesses that malicious actors could exploit proactively and provides actionable insights for remediation. Various tools and techniques are employed during vulnerability testing to scan and analyze the target system or application for potential vulnerabilities.
What are the 4 main types of security vulnerability
The four main types of vulnerabilities in information security are network vulnerabilities, operating system vulnerabilities, process (or procedural) vulnerabilities, and human vulnerabilities.
What are the 5 types of vulnerability
One classification scheme for identifying vulnerability in subjects identifies five different types-cognitive or communicative, institutional or deferential, medical, economic, and social. Each of these types of vulnerability requires somewhat different protective measures.
What are the 4 types of concept of vulnerability
The different types of vulnerability
According to the different types of losses, the vulnerability can be defined as physical vulnerability, economic vulnerability, social vulnerability and environmental vulnerability.
What are the 4 main types of vulnerabilities
The four main types of vulnerabilities in information security are network vulnerabilities, operating system vulnerabilities, process (or procedural) vulnerabilities, and human vulnerabilities.
What are the 3 components of vulnerability assessment
There are three dimensions of vulnerability: exposure, sensitivity, and adaptive capacity.
What does CVE vulnerability mean
Common Vulnerabilities and Exposures
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.