Who assigns CVE numbers
The Mitre Corporation
CVEs are assigned by a CVE Numbering Authority (CNA). While some vendors acted as a CNA before, the name and designation was not created until February 1, 2005. there are three primary types of CVE number assignments: The Mitre Corporation functions as Editor and Primary CNA.
WHO publishes CVEs
the MITRE corporation
Founded in 1999, the CVE program is maintained by the MITRE corporation and sponsored by the U.S. Department of Homeland Security (DHS) and the Cybersecurity and Infrastructure Security Agency (CISA).
What is the CVE vulnerability ID
A CVE ID is a unique, alphanumeric identifier assigned by the CVE Program. Each identifier references a specific vulnerability. The “Year” portion is the year that the CVE ID was reserved or the year the vulnerability was made public. The year portion is not used to indicate when the vulnerability was discovered.
What is CVE in vulnerability management
CVE stands for Common Vulnerabilities and Exposures. The system provides a method for publicly sharing information on cybersecurity vulnerabilities and exposures. What is the Difference Between CVE and CVSS CVE is the database of known vulnerabilities and exposures.
How are CVEs determined
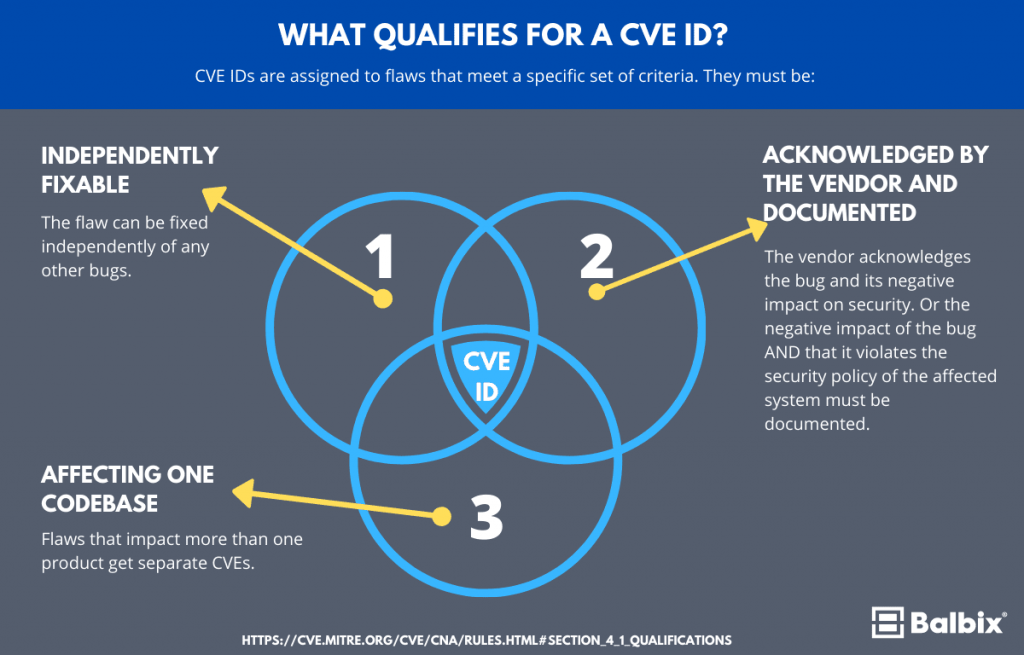
A flaw is declared a CVE when it meets three very specific criteria: The flaw can be fixed separately of any other bugs. The software vendor acknowledges and documents the flaw as hurting the security of its users. The flaw affects a singular codebase.
Who can request a CVE
Anyone can request a CVE ID for a vulnerability or request an update to an existing CVE Record. Learn more on the Process page.
Where are CVE published
the U.S. National Vulnerability Database
A CVE Record can change from the RESERVED state to being published at any time based on a number of factors both internal and external to the CVE List. Once the CVE Record is published with details on the CVE List, it will become available in the U.S. National Vulnerability Database (NVD).
How is a CVE created
The process of creating a CVE Record begins with the discovery of a potential cybersecurity vulnerability. The information is then assigned a CVE ID by a CVE Numbering Authority (CNA), a Description and References are added by the CNA, and then the CVE Record is posted on the CVE website by the CVE Program Secretariat.
Do all vulnerabilities have a CVE
CVE stands for Common Vulnerabilities and Exposures. It is the database of publicly disclosed information on security issues. All organizations use CVEs to identify and track the number of vulnerabilities. But not all the vulnerabilities discovered have a CVE number.
How does a vulnerability become a CVE listing
The process of creating a CVE Record begins with the discovery of a potential cybersecurity vulnerability. The information is then assigned a CVE ID by a CVE Numbering Authority (CNA), a Description and References are added by the CNA, and then the CVE Record is posted on the CVE website by the CVE Program Secretariat.
How is vulnerability determined
Physical Vulnerability may be determined by aspects such as population density levels, remoteness of a settlement, the site, design and materials used for critical infrastructure and for housing (UNISDR). Example: Wooden homes are less likely to collapse in an earthquake, but are more vulnerable to fire.
Who maintains the CVE list
MITRE, maintains the CVE dictionary and public website. It also manages the CVE Compatibility Program, which promotes the use of standard CVE identifiers by authorized CVE numbering authorities (CNAs).
How many CVE numbering authorities are there
CNA Program Growth
Currently, there are 307 CNAs (305 CNAs and 2 CNA-LRs) from 36 countries participating in the CVE Program.
What are the 4 stages of identifying vulnerabilities
A 4-Step Vulnerability Management ProcessIdentification. A vulnerability management system continuously scans an environment against one or more databases of known vulnerabilities, with the objective of identifying vulnerable assets.Prioritization.Remediation.Verification and Reporting.
What are the 3 criteria for assessing vulnerability
The assessment framework involves three dimensions: engagement, intent and capability, which are considered separately.
What is a CVE number and how is IT used in Pentest reporting
CVE is a glossary that classifies vulnerabilities. The glossary analyzes vulnerabilities and then uses the Common Vulnerability Scoring System (CVSS) to evaluate the threat level of a vulnerability. A CVE score is often used for prioritizing the security of vulnerabilities.
How are vulnerabilities determined
Modern vulnerability assessments rely on automated scanning tools. Here are the main categories of tools used to scan an environment for vulnerabilities: Network-based scanning—used to identify potential network security attacks. This type of scan can also detect vulnerable systems on wired or wireless networks.
Which are the 4 key drivers of vulnerability
4 key drivers of customer vulnerabilityHealth. Conditions or illnesses that affect one's ability to complete day-to-day tasks, both mentally and physically.Life Events. Such as bereavement, job loss or relationship breakdown.Resilience. Low ability to withstand and manage financial or emotional shocks.Capability.
How are security vulnerabilities identified
What are the sources to identify security vulnerability within an application Security scan of an application using third party tools. Regularly monitoring security vulnerabilities in related applications or environments (Operating System, Database, Third party libraries etc).
Who finds vulnerabilities
Vulnerabilities usually arise when a researcher or attacker discovers that part of a program's code can be forced to run in an unexpected way, which results in undesirable behavior.
What are the 3 factors that can create vulnerability
Vulnerability relates to a number of factors, including:Physical factors. e.g. poor design and construction of buildings, unregulated land use planning, etc.Social factors.Economic factors.Environmental factors.
What are the 3 components of vulnerability assessment
There are three dimensions of vulnerability: exposure, sensitivity, and adaptive capacity.
What determines vulnerability
The conditions determined by physical, social, economic and environmental factors or processes which increase the susceptibility of an individual, a community, assets or systems to the impacts of hazards.
How do attackers find vulnerabilities
Scanning can be considered a logical extension (and overlap) of active reconnaissance that helps attackers identify specific vulnerabilities. It's often that attackers use automated tools such as network scanners and war dialers to locate systems and attempt to discover vulnerabilities.
How are vulnerabilities detected
Vulnerability detection is the identification of software vulnerabilities across your systems. It identifies what the weaknesses are in the environment. These might be detected via database scans, application scans, host-based scans, and other scans.