When did TLS 1.2 become standard
2008
TLS 1.2 was released in 2008, offering improved security, and was designed for both high performance and improved reliability. To accomplish this, it relies on a combination of symmetric and asymmetric cryptography.
Is it recommended to disable TLS 1.1 and replace it with TLS 1.2 or higher
TLS 1.0 and TLS 1.1 are no longer considered secure, due to the fact that they are vulnerable to various attacks, such as the POODLE attack. Disabling TLS 1.0 and TLS 1.1 on your server will force clients to use a more secure protocol (TLS 1.2), which is less vulnerable to attack.
What version of TLS is standard
TLS 1.3
Thus the minimum commonly supported TLS version is 1.1; however, PCI-DSS and NIST strongly suggest the use of the more secure TLS 1.2 (and, as seen above, NIST recommends adoption of TLS 1.3 and plans to require support by 2024).
Should TLS 1.2 be used
While TLS 1.2 can still be used, it is considered safe only when weak ciphers and algorithms are removed. On the other hand, TLS 1.3 is new; it supports modern encryption, comes with no known vulnerabilities, and also improves performance.
When was TLS 1.2 deprecated
2 End of Life. It appears the maximum number of years is 22years and the average is approximately 15 years. TLS 1.2 being published in 2008 would then have an expected life of 22years to 2023 however we expect it to be longer than this.
Why was TLS 1.0 deprecated
There are also real security risks of using TLS 1.0 or 1.1 in any IT infrastructure or solutions. Well-known attacks like BEAST (Browser Exploit Against SSL/TLS), POODLE (Padding Oracle On Downgraded Legacy Encryption), etc.
Which TLS version is more secure
TLS 1.3
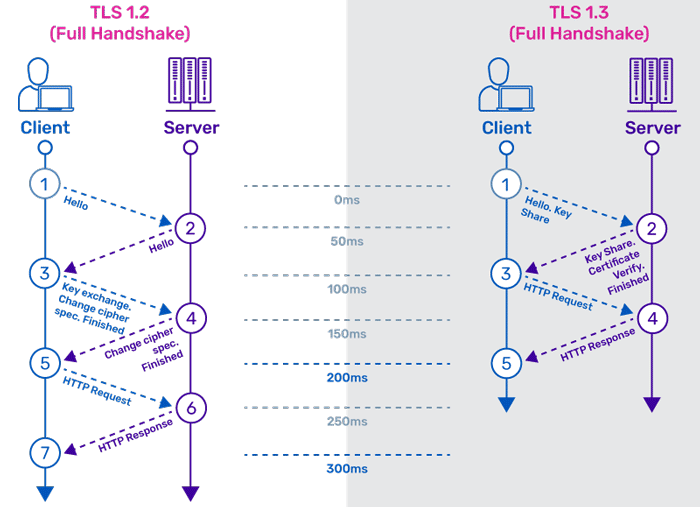
In a nutshell, TLS 1.3 is faster and more secure than TLS 1.2. One of the changes that makes TLS 1.3 faster is an update to the way a TLS handshake works: TLS handshakes in TLS 1.3 only require one round trip (or back-and-forth communication) instead of two, shortening the process by a few milliseconds.
Is TLS 1.2 deprecated
TLS 1.0 and 1.1 were deprecated by IETF in RFC 8996 datatracker.ietf.org/doc/rfc8996 in March 2021. AFAIK there is no plan to deprecate TLS 1.2 yet but a bunch of the ciphersuites it supports are deprecated.
Do PCI standards recommend using TLS 1.2 or higher
Overview. Both TLS 1.0 and TLS 1.1 are insufficient for protecting information due to known vulnerabilities. Specifically for Cloudflare customers, the primary impact of PCI is that TLS 1.0 and TLS 1.1 are insufficient to secure payment card related traffic. PCI standards recommend using TLS 1.2 or higher.
Which TLS version is better
In a nutshell, TLS 1.3 is faster and more secure than TLS 1.2. One of the changes that makes TLS 1.3 faster is an update to the way a TLS handshake works: TLS handshakes in TLS 1.3 only require one round trip (or back-and-forth communication) instead of two, shortening the process by a few milliseconds.
Why TLS 1.3 is not used
TLS 1.3 mandates the use of specific ciphers, which can take a toll on the server side. SSL offload on application delivery controllers (ADCs) and decryption on servers would require costly hardware upgrades and administrative overhead. TLS 1.2 is still relevant and has not yet been compromised.
When was SSL 2.0 deprecated
SSL 2.0: Launched in 1995 but has known problems with security. It was deprecated in 2011. SSL 3.0: Launched in 1996 but deprecated in 2015.
Has TLS 1.2 been compromised
Any software is going to have vulnerabilities – flaws that an attacker can exploit. In the case of TLS, parts of the protocol carried over from its early days in the 1990s resulted in several high-profile vulnerabilities persisting in TLS 1.2.
Why are TLS v1 0 and v1 1 no longer recommended
TLS 1.0 and 1.1 are vulnerable to downgrade attacks since they rely on SHA-1 hash for the integrity of exchanged messages. Even authentication of handshakes is done based on SHA-1, which makes it easier for an attacker to impersonate a server for MITM attacks.
Why is TLS 1.2 not secure
In TLS 1.2 and earlier versions, the use of ciphers with cryptographic weaknesses had posed potential security vulnerabilities. TLS 1.3 includes support only for algorithms that currently have no known vulnerabilities, including any that do not support Perfect Forward Secrecy (PFS).
Is TLS 1.2 the most secure
The most widely used versions of TLS nowadays are TLS 1.0, TLS 1.1, and TLS 1.2. While TLS 1.0 & TLS 1.1 are known to be very vulnerable, the TLS 1.2 protocol is considered to be much more secure and is thus recommended for use.
Is TLS 1.2 vulnerable
TLS 1.2 enables RSA-MD5 signatures for both client and server signatures. This flaw could be used to launch a man-in-the middle attack on a TLS 1.2 server-client connection. However, this kind of attack is typically more difficult to perform than client-authentication attacks.
What is the most commonly used TLS version
TLS 1.2
Based on TLS 1.1, TLS 1.2 was released by the IETF in 2008 with the RFC-5246. To date, it's the most commonly used TLS protocol version. It's supported by 99.9% of the websites analyzed by SSL Labs (as of January 2023).
What is the best minimum TLS version
1.1
Consider using TLS 1.0 or 1.1 for sites with a broad user base, particularly non-transactional sites. In this way, you minimize the possibility that some clients cannot connect to your site securely.
Which TLS version is safest
TLS 1.3
In a nutshell, TLS 1.3 is faster and more secure than TLS 1.2. One of the changes that makes TLS 1.3 faster is an update to the way a TLS handshake works: TLS handshakes in TLS 1.3 only require one round trip (or back-and-forth communication) instead of two, shortening the process by a few milliseconds.
Why is TLS 1.3 better
In a nutshell, TLS 1.3 is faster and more secure than TLS 1.2. One of the changes that makes TLS 1.3 faster is an update to the way a TLS handshake works: TLS handshakes in TLS 1.3 only require one round trip (or back-and-forth communication) instead of two, shortening the process by a few milliseconds.
Is SSL 2.0 still supported
SSL 2.0 was deprecated in 2011 by RFC 6176. In 2014, SSL 3.0 was found to be vulnerable to the POODLE attack that affects all block ciphers in SSL; RC4, the only non-block cipher supported by SSL 3.0, is also feasibly broken as used in SSL 3.0. SSL 3.0 was deprecated in June 2015 by RFC 7568.
Why is TLS 1.1 bad
TLS 1.0 and 1.1 are vulnerable to downgrade attacks since they rely on SHA-1 hash for the integrity of exchanged messages. Even authentication of handshakes is done based on SHA-1, which makes it easier for an attacker to impersonate a server for MITM attacks.
Which version of TLS is most secure
TLS 1.3 offers several improvements over earlier versions, most notably a faster TLS handshake and simpler, more secure cipher suites. Zero Round-Trip Time (0-RTT) key exchanges further streamline the TLS handshake. Together, these changes provide better performance and stronger security.
Does TLS 1.2 have vulnerabilities
Any software is going to have vulnerabilities – flaws that an attacker can exploit. In the case of TLS, parts of the protocol carried over from its early days in the 1990s resulted in several high-profile vulnerabilities persisting in TLS 1.2.