What is the difference between Log4j and log42
Log4j2 comes with many features that Log4j didn't have. Similarly, Log4j only supported configuration files in properties and XML formats, while Log4j2 supports configuration through XML, JSON, YAML, and configuration files/programmatic actions. In comparison to Log4j, Log4j2 has active community support.
What is the difference between Log4j 1 and Log4j 2
Community support: Log4j 1. x is not actively maintained, whereas Log4j 2 has an active community where questions are answered, features are added and bugs are fixed. Automatically reload its configuration upon modification without losing log events while reconfiguring.
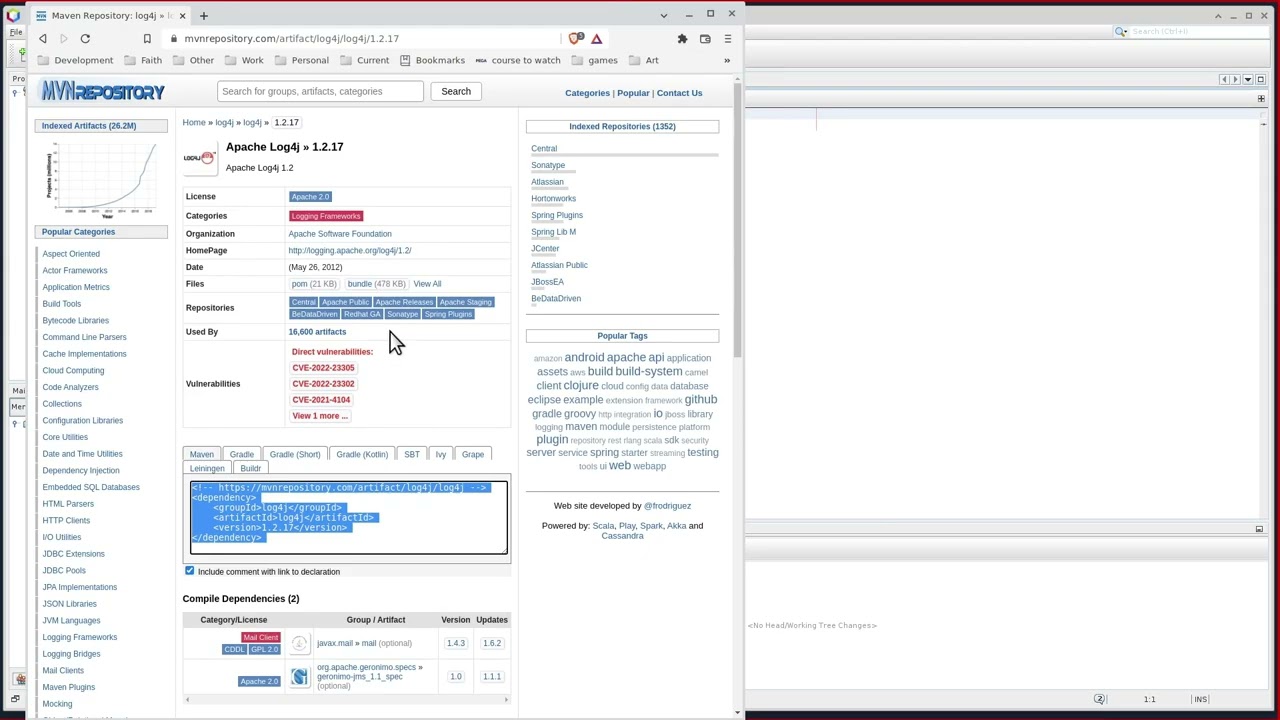
What is the version Log4j 1.2 17
Apache Log4j » 1.2. 17
| License | Apache 2.0 |
|---|---|
| Files | pom (21 KB) bundle (478 KB) View All |
| Repositories | CentralApache PublicApache ReleasesApache StagingBeDataDrivenHortonworksMulesoftOrekitRedhat GASonatypeSpring Plugins |
| Ranking | #16 in MvnRepository (See Top Artifacts) #3 in Logging Frameworks |
| Used By | 18,289 artifacts |
What versions of Log4j are supported
Apache Log4j
| Release | Released | Supported |
|---|---|---|
| 2 | 9 years ago (12 Jul 2014) | Yes |
| 2.12 | 4 years ago (26 Jun 2019) | Ended 1 year and 7 months ago (14 Dec 2021) |
| 2.3 | 8 years ago (10 May 2015) | Ended 7 years and 10 months ago (20 Sep 2015) |
| 1 | 22 years ago (08 Jan 2001) | Ended 7 years ago (15 Oct 2015) |
14 thg 6, 2023
Which Log4j version has vulnerabilities
Technical Details. The CVE-2021-44228 RCE vulnerability—affecting Apache's Log4j library, versions 2.0-beta9 to 2.14. 1—exists in the action the Java Naming and Directory Interface (JNDI) takes to resolve variables.
Which Log4j versions are vulnerable
What happened to log4j recently
| Name | Vulnerability type | Affected log4j versions |
|---|---|---|
| CVE-2021-45046 | Denial of Service (DoS) and RCE | 2.0 through 2.15.0 |
| CVE-2021-4104 | RCE | 1.2* |
| CVE-2021-45105 | Denial of Service (DoS) | 2.0-beta9 to 2.16.0 |
| CVE-2021-44832 | RCE | 2.0 to 2.17.0 |
Is Log4j 1.2 safe
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
What is Log4j bridge
The Log4j 1.2 Bridge allows applications coded to use Log4j 1.2 API to use Log4j 2 instead.
Is Log4j 1.2 17 Safe
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Does Log4j 1.2 have vulnerability
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
Is Log4j 1.2 12 vulnerable
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. How to fix Deserialization of Untrusted Data
Is Log4j 1.2 vulnerable
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
What is the vulnerability of Log4j 1.2 12
Affected versions of this package are vulnerable to Man-in-the-Middle (MitM). Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
Is Log4j 1 version vulnerable
x. JMSSink in Log4j 1. x is vulnerable to deserialization of untrusted data. This flaw allows a remote attacker to execute code on the server if the deployed application is configured to use JMSSink and to the attacker's JNDI LDAP endpoint.
Is Log4j 1.2 bridge vulnerable
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data.
Why is Log4j on my computer
Log4j is used by developers to keep track of what happens in their software applications or online services. It's basically a huge journal of the activity of a system or application. This activity is called 'logging' and it's used by developers to keep an eye out for problems for users.
Does Log4j 1.2 14 have vulnerability
Affected versions of this package are vulnerable to Deserialization of Untrusted Data. JMSSink in all versions of Log4j 1. x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to.
Is Log4j 1.2 end of life
Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions. CSM version 6.3.
Is Log4j a malware
Last week, a vulnerability was found in Log4j, an open-source logging library commonly used by apps and services across the internet. If left unfixed, attackers can break into systems, steal passwords and logins, extract data, and infect networks with malicious software.
Should I delete Log4j files
the vulnerability (the vulnerability was introduced starting in Log4j2), so there is no exploit risk. Removing these files can cause failures in Ant and issues with generating jar files used for custom/interception/transformation scripts. It is not recommended to remove these files.
Is 1.2 of Log4j vulnerable
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.
What is the vulnerability of Log4j 1.2 15
Affected versions of this package are vulnerable to Man-in-the-Middle (MitM). Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
Does Log4j vulnerability affect Log4j 1
Log4j 1.
x are only vulnerable to this attack when they use JNDI in their configuration. A separate CVE (CVE-2021-4104) has been filed for this vulnerability. To mitigate: Audit your logging configuration to ensure it has no JMSAppender configured. Log4j 1.
Does Log4j 1.2 have the vulnerability
JMSAppender, in log4j 1.2 version, is vulnerable to deserialization of untrusted data if the attacker has the 'write' permissions to the log4j configuration.